What is Patch Tuesday
Patch Tuesday refers to regular, scheduled releases of software patches and updates by various technology companies, including Microsoft, Adobe, Oracle etc. It occurs on the second Tuesday of each month. During Patch Tuesday, Microsoft releases:
Security Updates
Bug Fixes
Improvements in its products (Windows OS, MS Office, other supported MS applications)
Products
In the provided image below, we can see that the primary vulnerable products are Windows Kernel, Microsoft WDAC OLE DB provider for SQL, followed by Windows ODBC Driver.
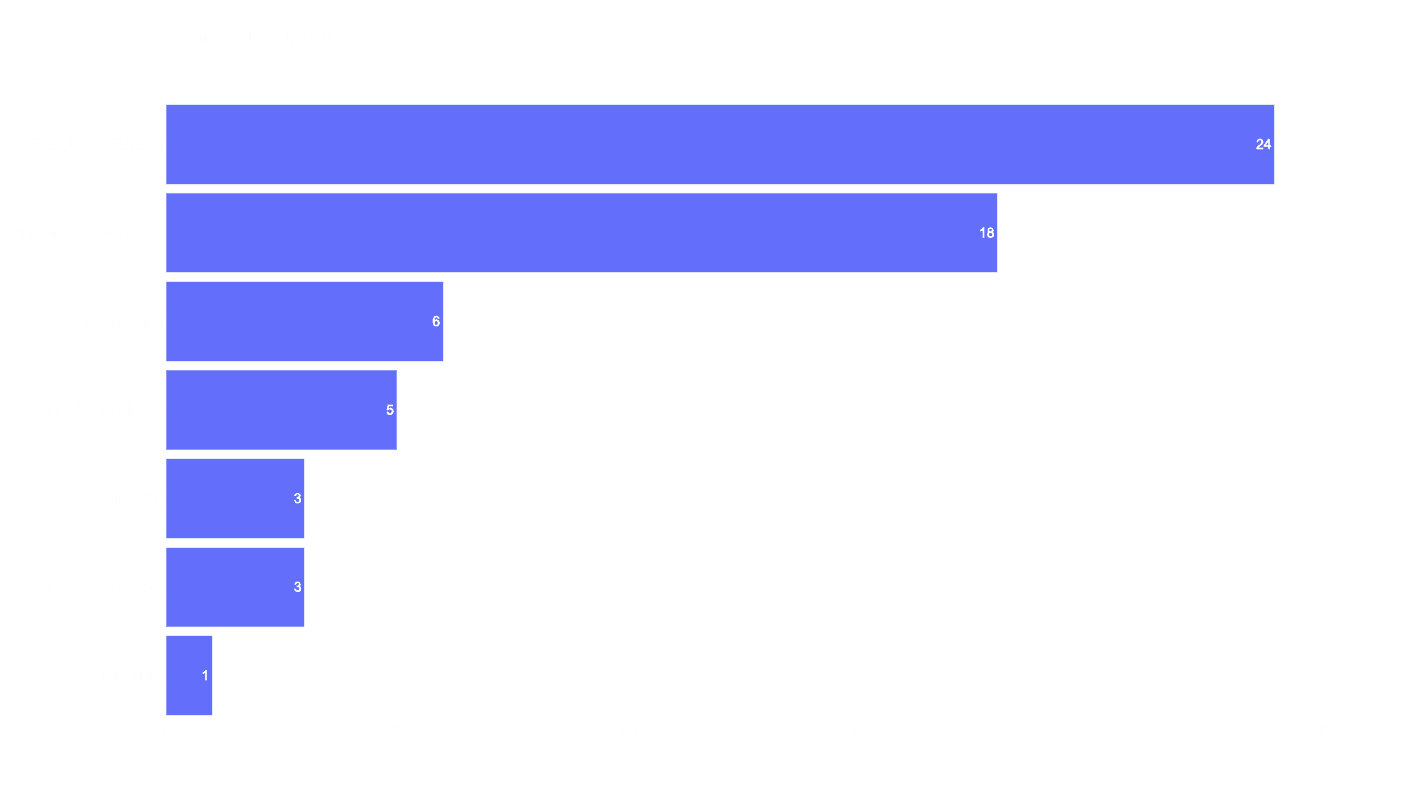
Vulnerability Types
In the image below we can observe that the predominant vulnerability type for this month is Elevation of Privileges (24), trailed by Remote Code Execution (18) and Denial of Service (6) respectively.
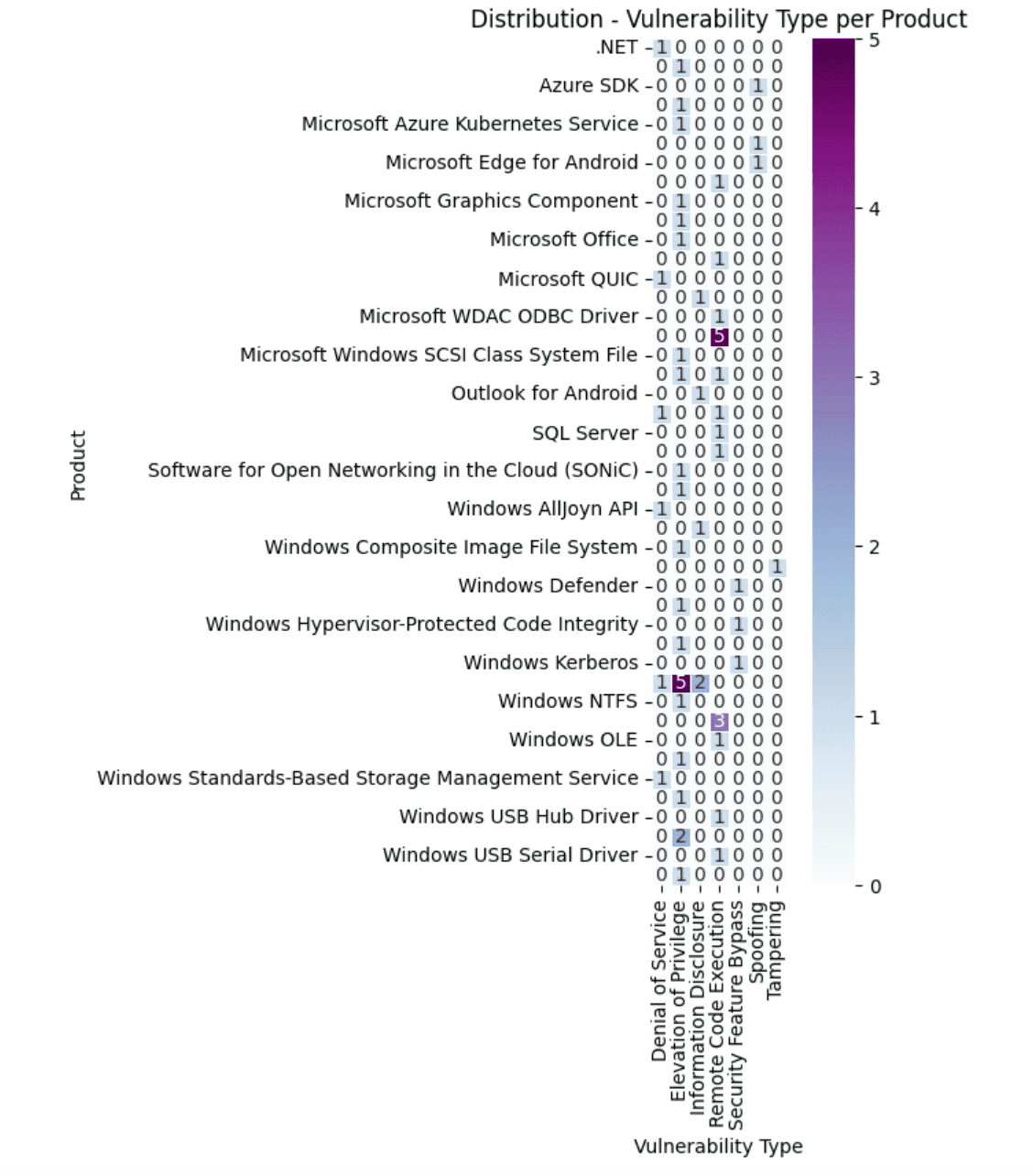
The below heatmap depicts the distribution of various vulnerability types per MS product.
CVSSv3 Score Distribution
It becomes evident that a significant majority of vulnerabilities gravitates towards the range of 7 to 9. This cluster underscores the high to critical severity of these vulnerabilities.
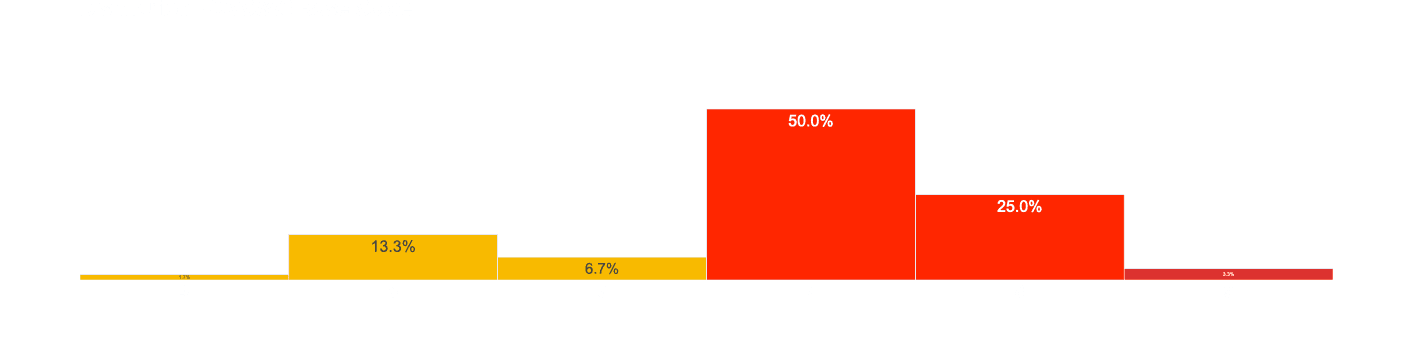
Statistics about CVSSv3 score distribution:
mean: ~7.5
min: 4.3
max: 9.8
25%: 7.0
50%: 7.8
75%: 8.8
median: 7.8
PRIOn KB Prioritization Decision Engine
PRIOn KB prioritization decision engine provides sensible default prioritization for vulnerabilities, which can also be customized to align with your security policies and requirements. The below horizontal bar chart provides a visual presentation of the distribution of vulnerabilities analysed via the PRIOn KB decision engine. At a glance, it becomes evident that the majority of the vulnerabilities, comprising a substantial 73.3% (44) of the total, fail into the “Significant” risk priority level. The “Routine” priority level makes up 26.7% (16) of the horizontal bar chart. At the time of writing, no urgent or immediate vulnerabilities identified and scored.
In the table below, we have arranged all the examined CVEs by priority.
CVE | Score | Label |
|---|---|---|
CVE-2024-21400 | 68 | Significant |
CVE-2024-21334 | 66 | Significant |
CVE-2024-21419 | 62 | Significant |
CVE-2024-21438 | 62 | Significant |
CVE-2024-21418 | 61 | Significant |
CVE-2024-21390 | 61 | Significant |
CVE-2024-21407 | 61 | Significant |
CVE-2024-21392 | 61 | Significant |
CVE-2024-21421 | 61 | Significant |
CVE-2024-21411 | 61 | Significant |
CVE-2024-21426 | 61 | Significant |
CVE-2024-21330 | 61 | Significant |
CVE-2024-21439 | 61 | Significant |
CVE-2024-21441 | 61 | Significant |
CVE-2024-21432 | 61 | Significant |
CVE-2024-21427 | 61 | Significant |
CVE-2024-21433 | 61 | Significant |
CVE-2024-21434 | 61 | Significant |
CVE-2024-21435 | 61 | Significant |
CVE-2024-21431 | 61 | Significant |
CVE-2024-21442 | 61 | Significant |
CVE-2024-21437 | 61 | Significant |
CVE-2024-21436 | 61 | Significant |
CVE-2024-26159 | 61 | Significant |
CVE-2024-21446 | 61 | Significant |
CVE-2024-21445 | 61 | Significant |
CVE-2024-21444 | 61 | Significant |
CVE-2024-21443 | 61 | Significant |
CVE-2024-26204 | 61 | Significant |
CVE-2024-26203 | 61 | Significant |
CVE-2024-26198 | 61 | Significant |
CVE-2024-26190 | 61 | Significant |
CVE-2024-26199 | 61 | Significant |
CVE-2024-21451 | 61 | Significant |
CVE-2024-26162 | 61 | Significant |
CVE-2024-26161 | 61 | Significant |
CVE-2024-26169 | 61 | Significant |
CVE-2024-26164 | 61 | Significant |
CVE-2024-26165 | 61 | Significant |
CVE-2024-26178 | 61 | Significant |
CVE-2024-26182 | 61 | Significant |
CVE-2024-26173 | 61 | Significant |
CVE-2024-26170 | 61 | Significant |
CVE-2024-26185 | 60 | Routine |
CVE-2024-26197 | 59 | Routine |
CVE-2024-21429 | 59 | Routine |
CVE-2024-21408 | 59 | Routine |
CVE-2024-20671 | 59 | Routine |
CVE-2024-26181 | 59 | Routine |
CVE-2024-21448 | 59 | Routine |
CVE-2024-26167 | 59 | Routine |
CVE-2024-26201 | 59 | Routine |
CVE-2024-26177 | 59 | Routine |
CVE-2024-26174 | 59 | Routine |
CVE-2024-21430 | 52 | Routine |
CVE-2024-21440 | 52 | Routine |
CVE-2024-21450 | 52 | Routine |
CVE-2024-26160 | 52 | Routine |
CVE-2024-26176 | 52 | Routine |
How PRIOn can help
PRIOn is an AI driven vulnerability prioritization technology. PRIOn is here to automatically prioritize vulnerabilities, public or private, that matter most across your entire environment. Contact us here for any inquiry/demo. We are here to assist you to transform your vulnerability management lifecycle.